Drive through any town in New Hampshire or Maine and you'll pass businesses we protect. Storefronts. Office buildings. Organizations you interact with every day, maybe without even thinking about it. We know their names. We know their systems. We know what they have to lose.
And that's exactly why you won't find their logos on our website.
Your IT provider's logo wall is a gift to hackers
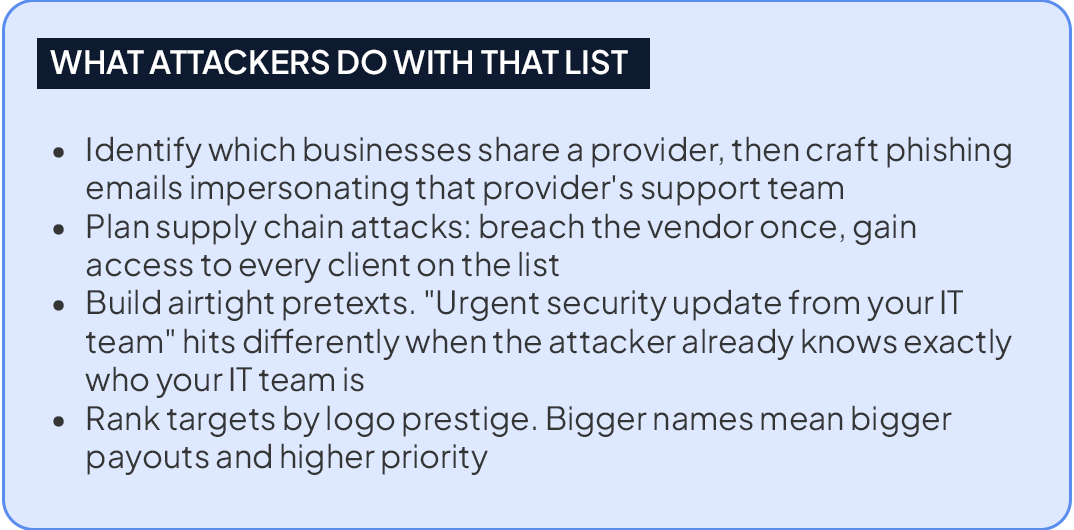
To a marketing team, a client logo wall is social proof. To a cybercriminal conducting reconnaissance, it's something far more useful: a verified, publicly posted map of exactly which businesses share the same IT provider, the same infrastructure, and potentially the same vulnerabilities.
Modern cyberattacks don't start with brute force. They start with open-source intelligence (OSINT), which means combing publicly available information to profile targets before a single line of malicious code is written. A vendor's client page is one of the most valuable things an attacker can find.
The attack that took down the internet and what it proved
In October 2016, one of the largest DDoS attacks in history hit a major DNS infrastructure provider, knocking dozens of high-traffic websites offline for hours across North America and Europe. The attacker didn't pick that target at random. They identified a single provider with a publicly known, high-value client base and hit the root
That's the supply chain playbook. You don't need to breach every company on the list. You just need to breach the one company they all trust. The logo wall told attackers exactly how much damage that one breach could do.
When your vendor advertises you, they're not just showing off. They're telling every threat actor online a list of exactly who's worth targeting.
Why we do things differently
One thing to do right now
Pull up your current IT or cybersecurity vendor's website. Is your logo on there? Is there a client list, a "trusted by" section, a case study with your name on it, a testimonial with your full name and company name in it?
If yes, ask them who authorized that and what their written policy is on client confidentiality. If they don't have a clear answer, that tells you everything you need to know about how seriously they take your security.
The best IT partners don't just protect your systems. They protect your exposure, including the exposure that comes from their own marketing.